General Information About TFGBV
Chapter 2: Where does TFGBV happen?
TFGBV can occur across many digital spaces, and using various different technologies. In this chapter, we will overview common digital platforms and devices which can facilitate or become settings for TFGBV.
Learning Objectives
- Know the different places and ways that TFGBV can happen.
- Be able to identify TFGBV as it presents in different forms.
Sometimes, when we hear the terms “online abuse” or “technology-facilitated violence” we make assumptions about what they mean.
For example, many people may only think these terms apply to cyberbullying (such as strangers making mean comments on social media posts); or even non-consensual image sharing (like a bully sending out an embarrassing photo of you to the whole school through an email blast).
Mobile Devices
Mobile phones, laptops and PC computers, tablets, and wearable technology (like Apple watches) etc.) can be used to facilitate TFGBV.
This can happen through calls, texts, video chats, image sharing, and apps. TFGBV can also be facilitated by the forced restriction of access to these devices.

Online and Social Media Platforms
Online and social media platforms allow people to create profiles, share content, and interact with others. TFGBV can occur through comments, messages, impersonation, or unwanted contact.
To help you think broadly, here are different types of online platforms where TFGBV can occur, with examples for each. But remember, this list is not exhaustive. As we have seen in the last 10 years, new platforms appear all the time!
Reflect
Think of different platforms that “online and social media platforms” might refer to. How many can you list?
Social Media Platforms
Social media platforms focus on personal networking, where users create profiles to connect with one another. Examples include: Instagram (Threads), Facebook (Facebook Messenger), YouTube, TikTok, Twitter/X, WhatsApp, Snapchat, LinkedIn.
How TFGBV shows up: Harassment in comments or DMs, impersonation, non‑consensual image sharing, monitoring through “last seen” or story views.
Online Chatrooms and Forums
Online chatrooms and forums are digital spaces for real-time or asynchronous communication, ranging from specialized support groups and niche communities to random video chats. Examples include: Twitch, Omegle, Discord, reddit, 4chan.
How TFGBV can show up: Targeted harassment, doxxing, grooming, coordinated attacks, pressure to share personal information.
Dating Apps
Dating apps are mobile apps or websites where users can create profiles with the goal of creating sexual, romantic or even platonic relationships. Examples include: Tinder, Hinge, Facebook Dating, Grindr, Badoo, OKCupid, Bumble.
How TFGBV can show up: Coercive messaging, catfishing, threats after rejection, pressure to share intimate images, location‑based stalking.
Online Gaming
Online gaming is the use of console games, PC games, or mobile games which include online, interactive elements. Examples include:
- Multiplayer online games such as League of Legends, Call of Duty, Fortnite, or Minecraft.
- Social and interactive worlds such as Club Penguin, Second Life.
- Online, user driven games such as Roblox.
How TFGBV can show up: Voice‑chat harassment, targeted attacks, grooming of younger players, coercion through in‑game relationships, monitoring through shared servers.

Rideshare and Delivery Apps
These are mobile-based platforms that connect users with others for transportation (rideshare) or delivery services (food, groceries, packages). These platforms can be used by the user or the service providers to track and stalk locations, or carry out other harms. Examples of these can include Uber or UberEats, Bolt, KROOZ, and Mr D.
Monitoring and Tracking Technologies
Tools designed for convenience or safety can be misused to track, monitor, or control someone’s movements or activities. Examples include:
- Computers and mobile devices: Accessing accounts, browsing history, or installed apps.
- GPS and trackers: Monitoring location through phones, vehicles, wearables, or standalone devices.
- Home security cameras: Viewing footage from doorbell cameras, nanny cams, or hidden cameras.
- Smart home systems: Controlling lights, locks, alarms, or appliances to intimidate or restrict movement.

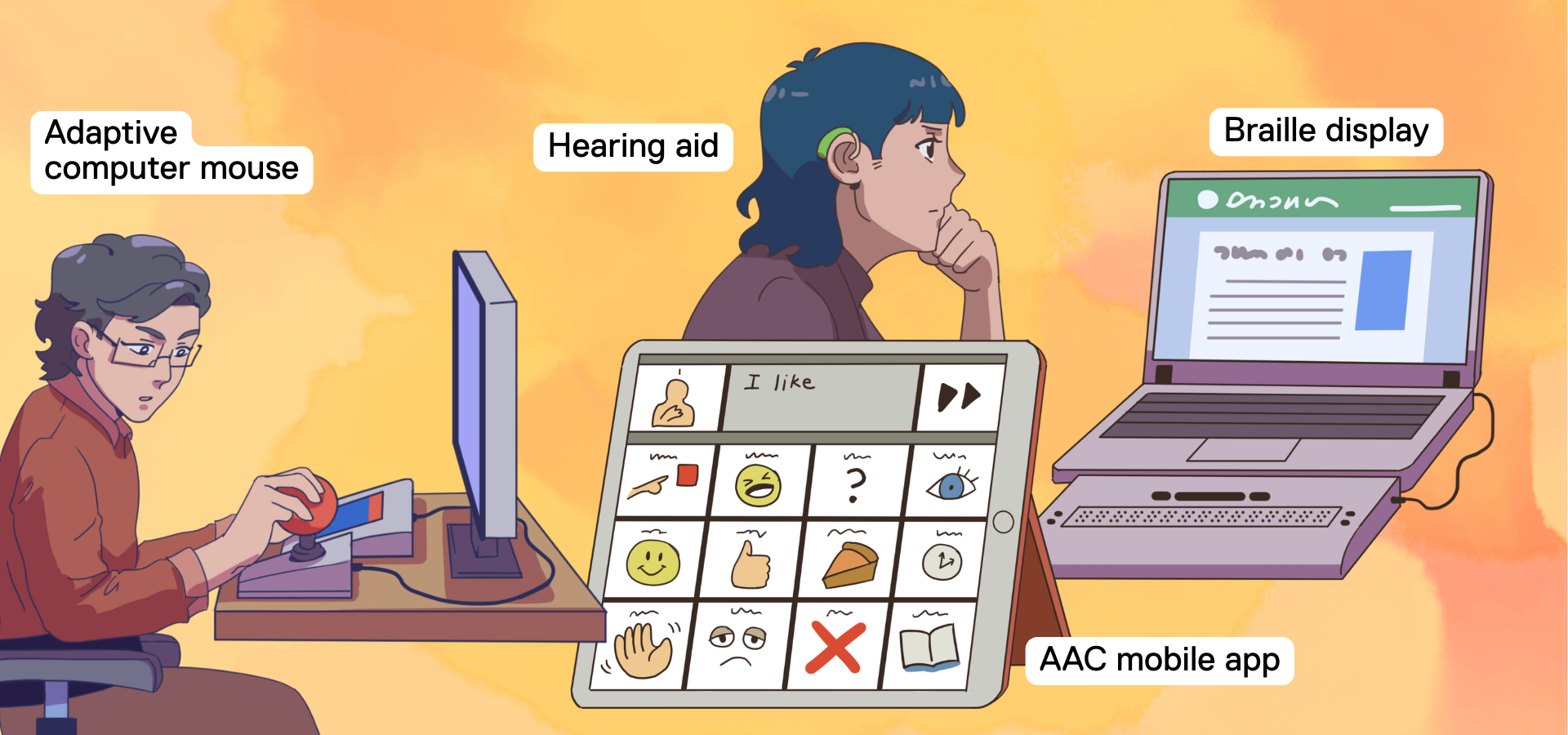
Assistive Technology
Assistive technologies are designed to support independence, communication, and access. When misused, they can become tools of surveillance, coercion, or control. This form of abuse is often invisible because the technology is assumed to be “helpful” and innocuous. Examples include:
- Screen‑readers: Monitoring what someone reads or accesses.
- Vision‑support apps: Accessing camera feeds or location data.
- Hearing aids with apps: Remotely adjusting or disabling devices, tracking usage.
- Augmentative and Alternative Communication (AAC) devices: Restricting access, deleting vocabulary, or monitoring communication.
Digital and Online Services
Everyday digital services hold sensitive personal information and can be used to commit TFGBV. Many services are not designed with accessibility or digital safety for people with disabilities in mind, and put people with disabilities at a greater risk of experiencing TFGBV.
Banking and Financial Services
Mobile and online banking platforms store financial data, transaction histories, and identity information. This is very private personal information.
How TFGBV can show up: Unauthorized access, financial control, monitoring spending or travel, coercion to share login details.
Healthcare, eHealth, and Telehealth Platforms
Healthcare is transitioning into online spaces, which is a great option for many people with disabilities who struggle to attend in-person appointments due to barriers in their physical environments. However, digital health systems contain sensitive information, which, if misused by the wrong people, can be dangerous.
How TFGBV can show up: Accessing private health records, tracking appointments or medications, impersonating someone to cancel care or obtain information.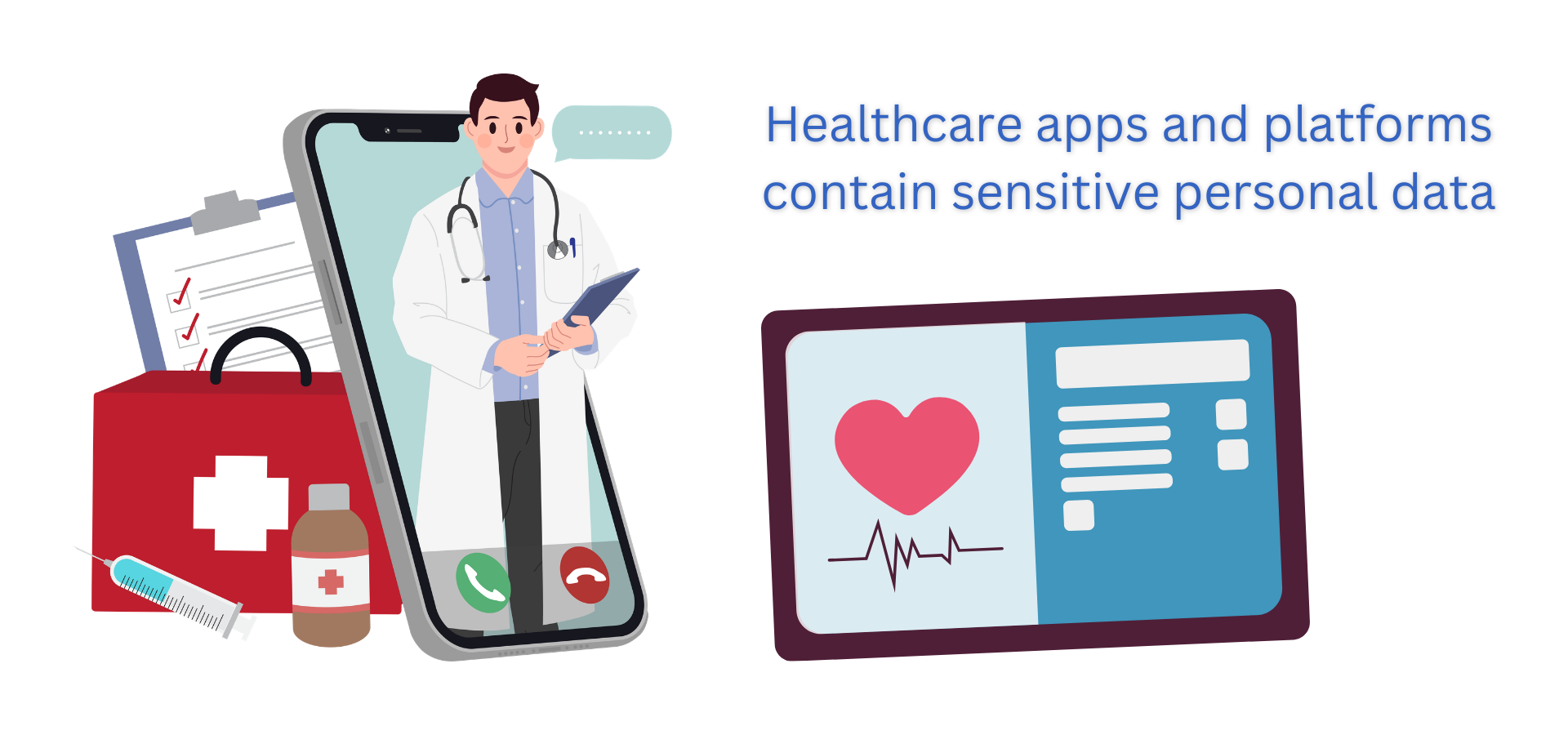
AI Chatbots and Generative Tools
Artificial intelligence (AI) is growing more powerful and prevalent in everyday life.
How TFGBV can show up: Creating fake messages or images, generating manipulated sexual content, automating harassment through bots.

Email Services
Email services such as Gmail, Yahoo!, Hotmail, Microsoft Outlook (et cetera), remain a very important central communication tool.
How TFGBV can show up: Account takeover, monitoring other linked services, resetting passwords to gain control.
Video Conferencing Platforms
These apps or platforms are used for video conferencing or calls, to facilitate digital communication. Examples include: Zoom, Google Meets, Microsoft Teams, Slack.
How TFGBV can show up: Joining calls without consent, recording or screenshotting meetings, harassing participants within calls, monitoring who someone speaks to.

Reflection
What other examples of TFGBV can you think of? Leave them in the comments below to educate us and others!
Activity



Feedback/Errata