General Information About TFGBV
Chapter 3: Forms of TFGBV
In this chapter, we will focus on the forms of TFGBV. This means, the actual behaviours and tactics that perpetrators use. The same harmful behaviours can appear across many different platforms, and that the same platform can be misused in several different ways. Separating the forms of TFGBV from potential places where TFGBV can occur makes it easier to recognise patterns, understand risks, and connect what you learn to real‑life situations.
When we listed platforms and devices in Chapter 2, our goal was to help you understand where tech‑facilitated gender‑based violence can take place. People use many different apps, websites, and digital tools every day, and any of them can be misused. But knowing the platforms alone doesn’t give the big picture story.
Learning Objectives
- Learn how TFGBV can be committed in different forms and with different tactics.
This chapter builds on the foundation from Chapter 2 by showing how digital spaces can be used to harm someone. It gives you a clearer picture of what TFGBV can look like in practice, no matter which platform or device is involved.
There are hundreds of recognized forms of TFGBV, and TFGBV is constantly evolving. As a result, this list is not totally comprehensive. However, we will discuss the following common categories of TFGBV forms:
- Control-based abuse
- Cyber-grooming
- Economic and financial abuse
- Hacking and account takeovers
- Hate speech
- Image-based abuse
- Impersonation and identity theft
- Online harassment and cyberbullying
- Stalking, tracking, and digital surveillance
- Threats and intimidation
Control-Based Abuse
Control‑based abuse happens when someone restricts your ability to use phones, computers, the internet, or other technology. This can isolate someone from support or limit their independence. This may look or sound like:
- Taking away devices without consent or permission.
- Logging into accounts to monitor or restrict communication.
- Controlling devices under the excuse of “helping” or saying things like: “you don’t understand technology.”
- Limiting access to assistive technology needed for independence.
- Discouraging online presence with statements such as: “You’ll embarrass yourself online.

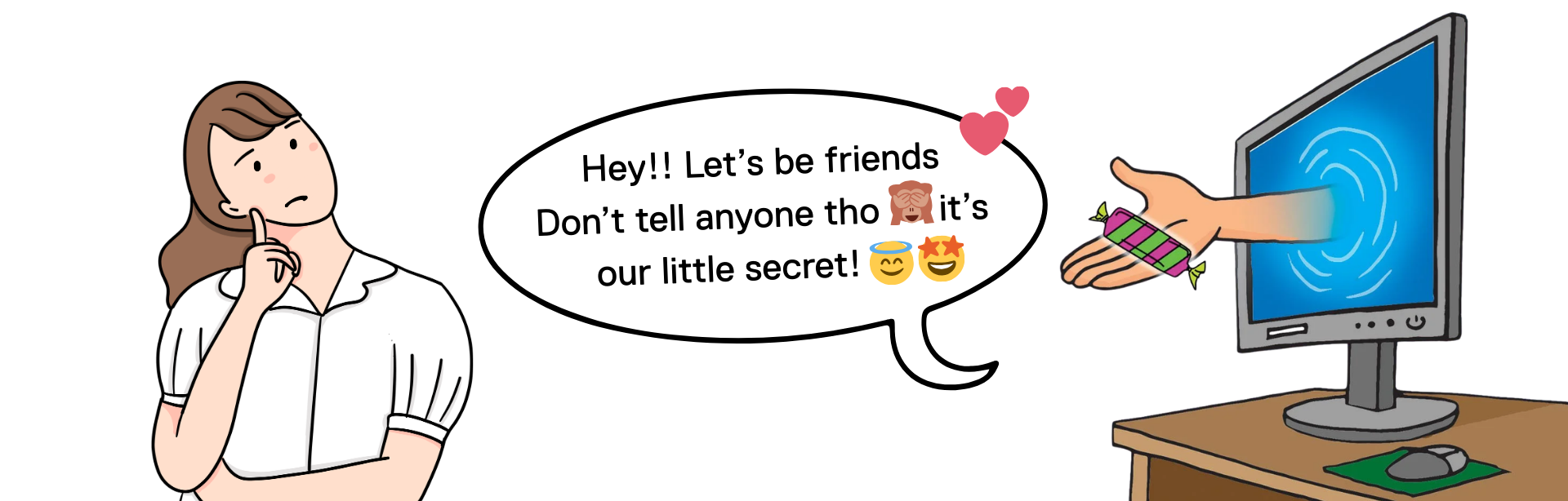
Cyber‑Grooming
Cyber‑grooming occurs when someone builds trust online to exploit another person sexually, financially, or emotionally. Grooming usually happens over time and often involves someone older or in a position of power (for example, a teacher, caregiver, or community leader). Cyber-grooming can include:
- Pretending to be a friend, romantic partner, or supportive figure.
- Using trust to pressure someone into harmful or abusive behaviour.
- Manipulating someone into giving money or access to financial resources.
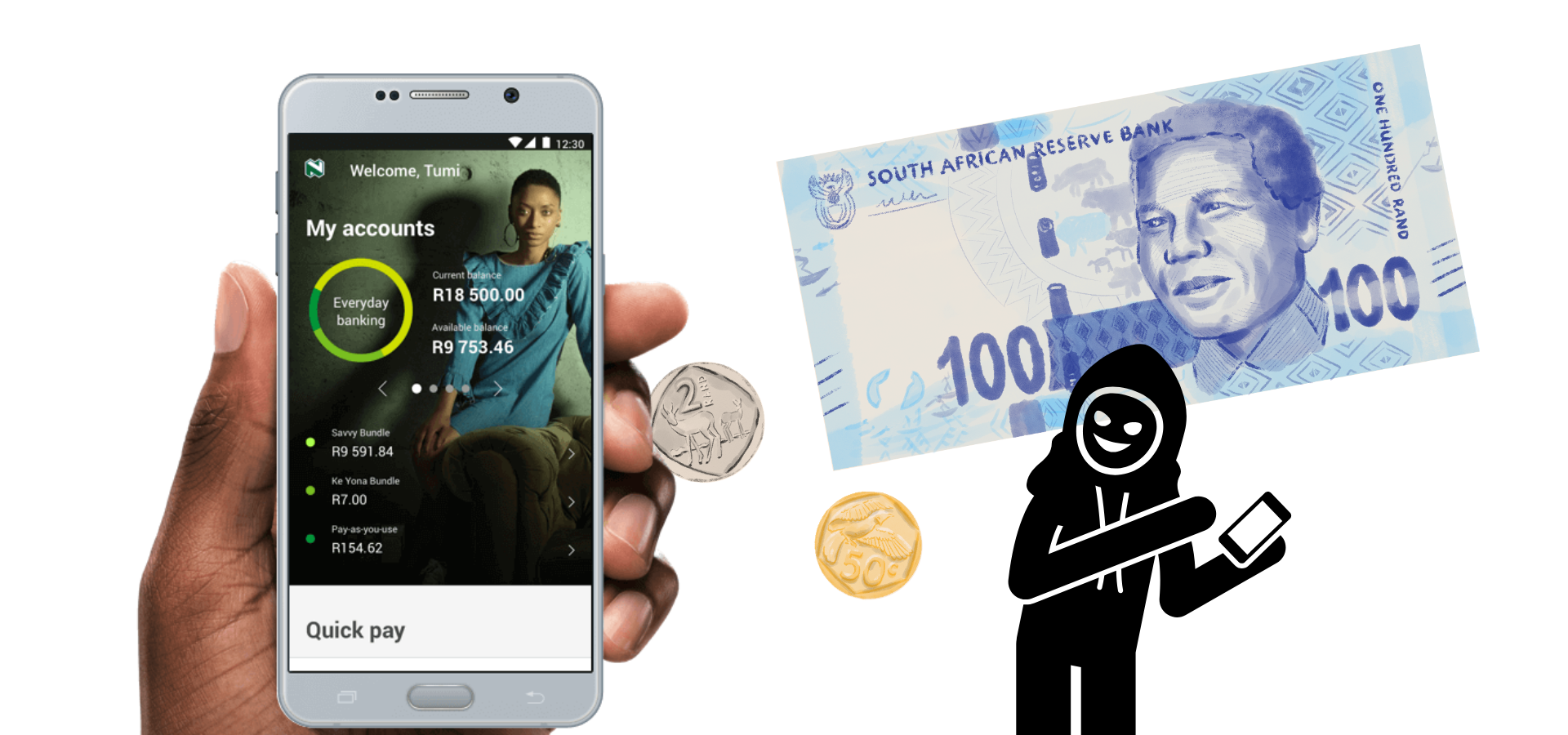
Economic and Financial Abuse
Digital platforms can be used to control or exploit someone’s finances. Examples of financial abuse may include:
- Accessing online banking without permission.
- Threatening harm unless money is sent.
- Offering “help” with finances as a way to gain control.
- Controlling disability payments or benefits.
- Forcing mobile money transfers.
- Locking someone out of financial or work‑related apps.
Hacking and Account Takeovers
Hacking involves accessing someone’s accounts, devices, or personal information without permission. This can include guessing passwords, using saved logins, or exploiting security weaknesses. Once inside an account, they may:
- Read private messages.
- Lock someone out.
- Impersonate them.
- Monitor activity.
Hacking often leads to other harms, such as financial abuse or impersonation.
Hate Speech
Hate speech targets someone’s identity, like their gender, disability, sexuality, or race. Hate speech can be used to shame, intimidate, or silence them. It can happen in online comments, messages, posts, gaming chats, or group discussions. Because it spreads quickly and publicly, it can cause significant emotional harm and reinforce discrimination.
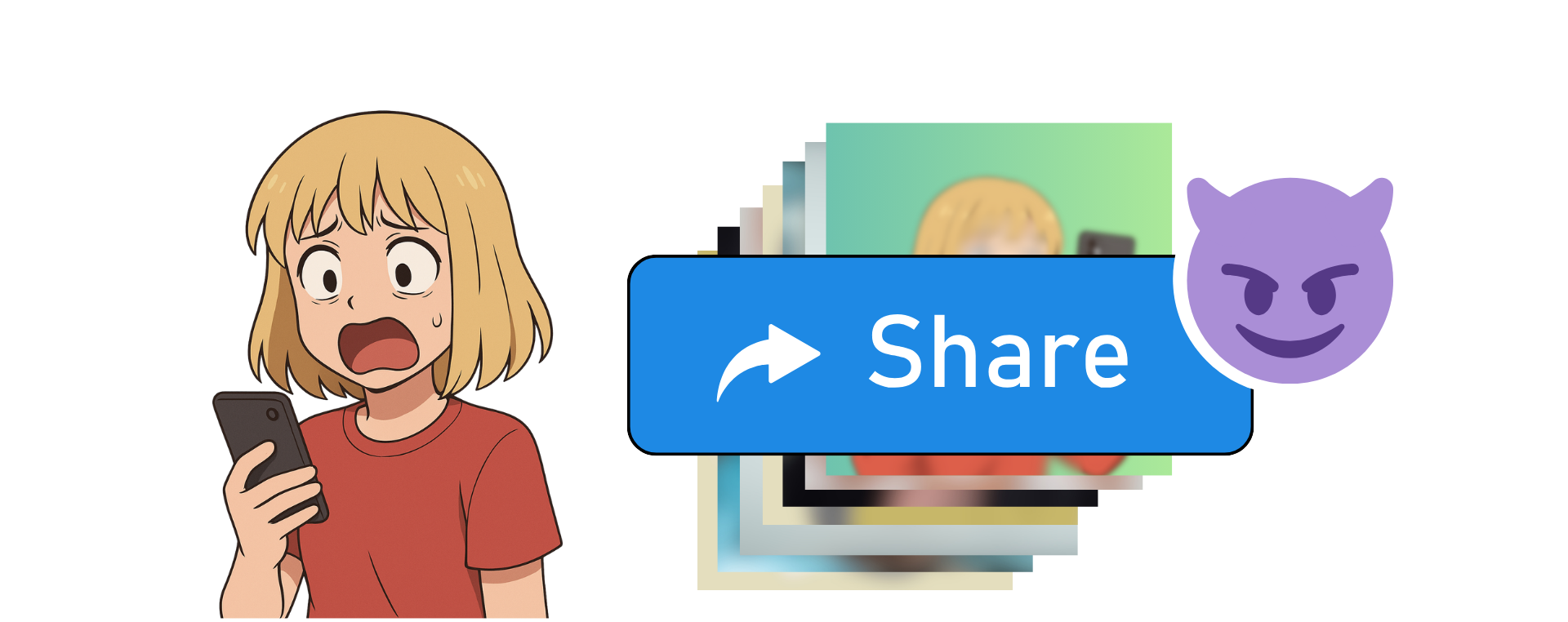
Image‑Based Abuse
Image‑based abuse involves creating, sharing, or threatening to share intimate or personal images without consent. Image-based abuse can include:
- Sharing someone’s intimate images without permission.
- Threatening to release personal images to coerce or control.
- Pressuring someone to send sexual images.
- Creating manipulated or deepfake images to shame or intimidate (“deepfakes”).
- Sending unwanted sexual images.
If you have experienced image based abuse, the StopNCII.org is a site that specifically provides resources and information for people who have experienced Non-Consensual Intimate Image abuse. For resources specific to South Africa, you can check our Support and Resources Page.
Impersonation and Identity Theft
Online impersonation occurs when someone pretends to be another person online, often to harm, deceive, or exploit them. Impersonation or identity theft may look like:
- Creating fake accounts using someone’s name or photos.
- Posting harmful or offensive content while pretending to be them.
- Messaging a target’s family or friends to request money under false pretenses.
- “Catfishing” by pretending to be someone else for romantic or financial gain.

Online Harassment and Cyberbullying
Online harassment includes repeated or targeted behaviour intended to cause emotional, social, or psychological harm. Cyberbullying often involves individuals or groups using their power to target someone. Examples include:
- Threatening or harassing messages.
- Disability‑based hate speech and ableism.
- Gendered hate speech, misogyny, homophobia, or transphobia.
- Spreading false information to damage reputation or cause distress.
See Case Study 1, to learn about Thandi’s experience with cyberbullying and harassment.

Stalking, Tracking, and Digital Surveillance
Digital tools can be misused to monitor someone’s movements, communications, or daily activities. These behaviours often involve repeated, unwanted contact or observation that causes fear or distress. Examples of surveillance or stalking include:
- Installing spyware under the guise of “helping.”
- Tracking location through phones, apps, or social media features.
- Monitoring home cameras, doorbell cameras, or other connected devices.
- Using vehicle GPS systems to follow someone’s movements.
- Justifying surveillance with statements such as “I need to keep an eye on you.”



Threats and Intimidation
Threats can be sent through any digital channel. They may involve threats of physical harm, threats to release personal information, or threats to damage someone’s reputation. Even without physical contact, digital threats can create fear, isolation, and ongoing emotional distress.
Reflection
Have you heard these forms of TFGBV before? Have you ever experienced them?
Which form of TFGBV do you think is most hidden for disabled women?
Resources
- Herrman, J. (2020, January 19). Who’s Watching Your Porch? The New York Times. https://www.nytimes.com/2020/01/19/style/ring-video-doorbell-home-security.html.
- Hinduja, S. (2025, December 29). Cyberstalking. Cyberbullying Research Center. https://cyberbullying.org/cyberstalking.
-
Fontes, L. A. (2024, August 7). Abusers Are Monitoring and Spying on Victims Through Their Cars. DomesticShelters.Org; DomesticShelters.org. https://www.domesticshelters.org/articles/identifying-abuse/abusers-are-monitoring-and-spying-on-victims-through-their-cars.


Feedback/Errata